Govern The Digital Assets and Apps Your Teams Build
Your business runs on hundreds of tools, combined by teams and AI-agents, in architectures nobody ever documented.
Supports hundreds of low-code, no-code, pro-code, automation and AI tech used by your teams
TrustedStack Makes Sense. See What's Really Running Your Business.
Effective governance and security require Discovery, Context, and Collaboration. We make the experience frictionless and continuous.
Continuous Discovery
Discover hundreds of building blocks, with deep insights on posture, tools and tech used to build Business Applications
Contextual Governance
Allow citizen-devs and Ops teams to manage theirs Stacks, while SecOps enforces security and compliance policies
Vendors
Discover & Manage
Discover hundreds of low/no-code, SaaS, AI, automation and other tech used by teams and systems. Explore and add new tech to your inventory from the TrustedStack™ Tech Hub.
Deep Tool & Vendor Intel
Up-to-date data on tools & vendors including verified detected risks, compliance posture, vendor infrastructure resilience, recent incidents & breaches, and more.
Business Apps Context
Go beyond undocumented technical architectures. Understand business-solution that were built using AI, integrations, automations and many low/no-code (LCNC) technologies.
Cross-team collaboration without friction.
CIO, CSO, GRC, CTO, Ops: Clear business-context and policies mean collaboration without friction, no Shadow-IT.
Cross-team Collab
CIO, CSO, GRC CTO, Ops: Clear business-context and policies mean collaboration without friction, no Shadow-IT
#TrustedStack [RevOps]
- TA
TrustedStack Auditor
- MY
Mark Young
- TA
TrustedStack Auditor
AI Governance & Control
Take control & maximize SAFE adoption of AI technologies and supply-chain with AI discovery and policies
Output Delivery
AI-generated content delivered to end users via API or interface.
- Data flows to customer systems
- Output validation required
AI Processing
Core-AI tools process data through LLMs, vector DBs, and RAG systems.
- Claude processes request
- Vector search retrieves context
Data Input
Customer data enters through forms, APIs, or integrations from SaaS tools.
- PII data identified
- Data retention policy checked
Security & Ops Insights
Security & operational Insights: detailed security events and broken workflows, by users, teams, the business-apps they build and scoped access to data.
Agile Governance Policies
Attribution-based governance policies are factoring app criticality, data-context, team, external/internal exposure, and other parameters, combined with automated response.
Secure LCNC + AI Usage
Guardrails to unsafe Shadow-IT by providing and enforcing security for devs and non-dev builders and operators who use low/no-code, automation & AI technologies.
Unparallel set of capabilities.
TrustedStack™ allows the CIO, CSO, CTO, and their teams to be agile, securely embracing tech, while aligning with what X-Ops teams build.
Discover & Manage
Discover hundreds of low/no-code, SaaS, AI, automation and other tech used by teams and systems. Explore and add new tech to your inventory from the TrustedStack™ Tech Hub.
Deep Tool & Vendor Intel
Up-to-date data on tools & vendors including verified detected risks, compliance posture, vendor infrastructure resilience, recent incidents & breaches, and more.
Business Apps Context
Go beyond undocumented technical architectures. Understand business-solution that were built using AI, integrations, automations and many low/no-code (LCNC) technologies.
Security & Ops Insights
Security & operational Insights: detailed security events and broken workflows, by users, teams, the business-apps they build and scoped access to data.
Agile Governance Policies
Attribution-based governance policies are factoring app criticality, data-context, team, external/internal exposure, and other parameters, combined with automated response.
Secure LCNC + AI Usage
Guardrails to unsafe Shadow-IT by providing and enforcing security for devs and non-dev builders and operators who use low/no-code, automation & AI technologies.
DORA & ISO 42001: Continuous Compliance, Not Checkbox Audits
DORA mandates ICT risk management, incident reporting, resilience testing, and third-party oversight for financial entities. ISO 42001 establishes the global standard for AI management systems, ensuring responsible development, deployment, and governance of artificial intelligence. TrustedStack™ maps both frameworks against your actual technology stack, continuously tracking vendor compliance, surfacing gaps in your supply chain, and generating audit-ready evidence without manual spreadsheets.
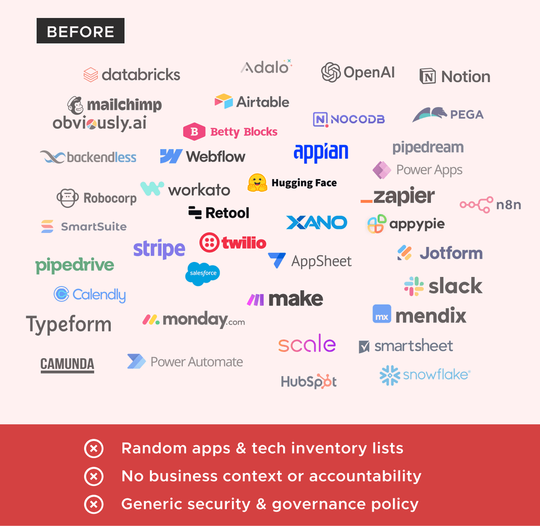
Before & After TrustedStack™
Hundreds of tools and technologies are used to build business solutions, but without context it is nearly impossible to effectively enforce security, compliance, and operational policies.
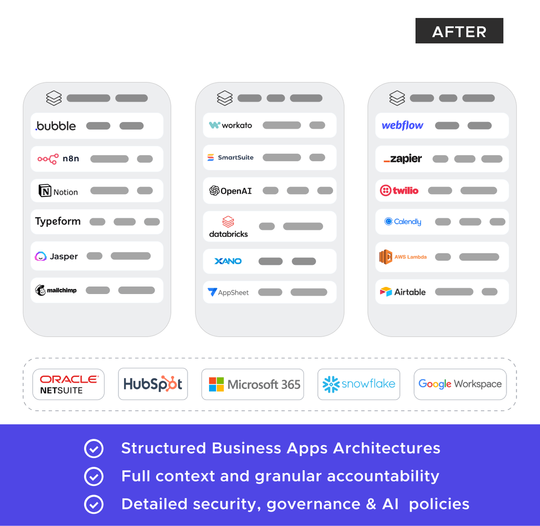
Integrates with all the tools you already know
Integrates with your business applications and many low-code, no-code, automation, and other tools your teams are using to run your business.
Designed for IT, Sec and Ops cross-team collaboration
CIO & CTO Teams
Provide a complete view of the technologies used by teams across the organization to build business solutions. Identify Security & Operational excellence and challenges.
CSO & GRC Teams
Simplify the task of continuously mapping technology use, finding gaps, and handling shadow IT by adding business context to security audits, including AI- usage, across the vendor supply chain
x-Ops Teams
Guarantee the operational efficiency and security of multi-tool stacks used by various teams. Respond quickly to issues with products, automation, and human operators.
Enterprise-grade Security
As security practitioners, our customers' security is always a top priority.
yes-security Inc. and the TrustedStack™ infrastructure and operations are
SOC 2 Type II certified and externally audited.
Frequently Asked Questions
Ready to get started?
Claim your free TrustedStack™ Audit today.
Uncover unparalleled insights into the security and compliance of your low-code/no-code (LCNC), automation, AI, and other tech-driven applications. Elevate your business with TrustedStack™!